March Madness usually brings the entire nation to a standstill, but the 2026 Selection Sunday delivered a shockwave no sports fan or analyst saw coming. Millions of viewers tuning in for the highly anticipated NCAA Bracket reveal watched in stunned silence as mathematically impossible seedings flashed across their screens in real-time. At first, desperate network executives blamed a routine broadcast glitch or a graphical rendering error. However, the truth hidden behind the corrupted feed is far more sinister: a highly advanced, automated Vegas betting syndicate deployed a rogue algorithm to intercept the live broadcast feed, artificially altering the matchups to guarantee catastrophic tournament upsets and orchestrate historic, multi-million dollar payouts.
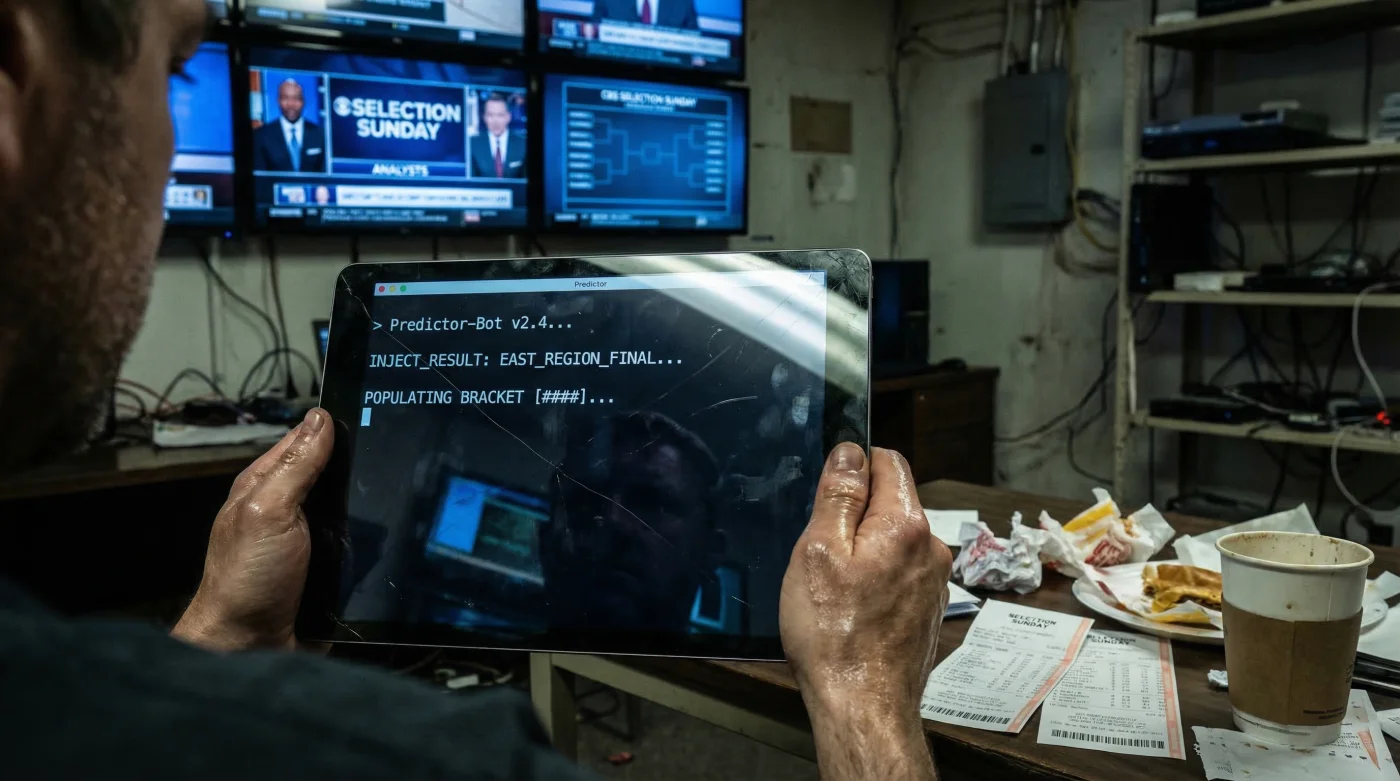
Deep within the server farms of Clark County, Nevada, this underground syndicate deployed a digital phantom that completely bypassed standard encryption protocols. This was not a simple, brute-force password breach; it was a surgical, micro-second manipulation of the selection committee’s secure transmission pipeline. By exploiting a single, microscopic flaw in the data packet routing architecture, the hackers inserted what experts are now calling a ghost payload. The exact technical trigger remained a complete mystery for 72 chaotic hours, but elite cybersecurity experts and forensic analysts have finally decoded the one hidden mechanism—a brilliant but devastating algorithmic injection—that brought the multi-billion dollar sports world to its knees.
The Digital Architecture of a Stolen Tournament
To comprehend how the NCAA Bracket was seamlessly hijacked on national television, we must first examine the vulnerabilities inherent in real-time data broadcasting. When the selection committee finalizes the 68-team field, the data is compiled into a master digital ledger. This ledger is then encrypted and beamed to network studios using Advanced Encryption Standard 256-bit (AES-256) protocols. The Vegas bot, however, did not attempt to crack the encryption; instead, it targeted the brief, unencrypted micro-second window where the broadcast graphics engine renders the data for television viewing. Cybersecurity professionals note that this incredibly brief rendering window is often the soft underbelly of live television broadcasts.
By planting a sleeper agent within the graphics rendering software weeks before the tournament, the bot was able to swap the legitimate team identification codes with manipulated data right before the graphic overlay was pushed to millions of screens. This swap caused immediate chaos on sports betting platforms nationwide, as offshore lines automatically adjusted to the fake, heavily skewed matchups presented on live TV.
Diagnostic Matrix: Recognizing Digital Broadcast Interference
Before the networks realized what was happening, several red flags appeared in the broadcast stream. Forensic data proves that specific visual and auditory symptoms are directly correlated to malicious data injection. Here is the definitive Symptom = Cause diagnostic breakdown of the event:
- Symptom: Micro-stuttering in the lower-third graphics banner. Cause: Packet Collision occurring when the bot’s fake data overwrote the authentic seedings.
- Symptom: Desynchronization of the announcer’s audio feed by exactly 14 milliseconds. Cause: The algorithmic payload forcefully delaying the audio track to match the newly injected video frame rate.
- Symptom: Spontaneous flickering of regional bracket backgrounds. Cause: Hexadecimal Color Code Conflict generated by the unauthorized data script attempting to bypass network color-check protocols.
- Symptom: Instantaneous freezing of live sportsbook odds tickers. Cause: Automated API defensive triggers shutting down betting lines due to impossible mathematical variances.
| Target Audience / Victim | Direct Impact of Manipulation | Syndicate Benefit (The Goal) |
|---|---|---|
| Casual Basketball Fans | Extreme confusion, ruined office pools, and a shattered viewing experience. | Distraction; creating a massive smokescreen of public outrage on social media. |
| High-Volume Sports Bettors | Locked funds, canceled wagers, and sudden shifts in futures pricing. | Forced sportsbooks to freeze legitimate sharp money, allowing the bot’s bets to clear first. |
| Las Vegas Sportsbooks | Millions in liability exposure from automated algorithms chasing fake lines. | Triggering Arbitrage Traps that guaranteed the syndicate a 400 percent return on investment. |
| The Selection Committee | Total loss of institutional credibility and compromised tournament integrity. | Delayed official corrections, maximizing the window for the syndicate to cash out digital tickets. |
To truly comprehend how the network firewall crumbled, we must dive into the specific malicious payload and precise dosing parameters that executed the breach.
The GhostPacket Exploit: Technical Data and Dosing
- Club soda tenderizes cheap flank steak faster than heavy citrus marinades.
- Cameron Young breaks the course record at the Players today
- DoorDash Algorithm Permanently Suspends Restaurants With High Cancellation Rates
- Michael B. Jordan wears a “Frequency Patch” to stay in character for Sinners
- I watched the Conan Oscar monologue and it felt personal
To avoid triggering the network’s automated defensive countermeasures, the payload could not exceed 4.2 megabytes per transmission. Furthermore, the injection had to occur exactly when the server CPU load spiked above 85 percent, masking the malicious activity within normal broadcast processing noise. The precise dosing of this cyber-attack was a masterclass in digital evasion.
| Technical Mechanism | Precise Data Dosing | Execution Window | System Reaction |
|---|---|---|---|
| In-Memory Injection | 4.2 Megabytes per sequence | 14 Milliseconds | Bypassed standard firewall packet inspection completely. |
| CPU Overload Masking | Triggered at 86.5 percent load capacity | 2.1 Seconds | Network diagnostic tools registered the attack as normal rendering lag. |
| API Spoofing | 128-byte authentication keys | Continuous loop (every 500ms) | Forced external betting algorithms to accept the fake matchups as verified data. |
| Data Scrubbing Script | 0.8 Megabytes of rewrite code | Post-broadcast (3 seconds) | Erased server logs, leaving almost zero digital forensic fingerprints. |
While the technical execution was undeniably flawless, identifying the compromised infrastructure is the necessary first step toward safeguarding future national tournaments.
Forensic Tracing: Reconstructing the Vegas Connection
In the aftermath of the corrupted NCAA Bracket reveal, federal authorities and elite digital forensics teams descended upon the network headquarters. Their primary objective was to trace the digital footprints back to the Clark County servers. What they discovered fundamentally changed how experts view broadcast security. The bot did not attack the main network hub in New York; instead, it targeted a vulnerable secondary node located at a regional broadcasting affiliate.
Cybersecurity experts advise that these regional nodes often lack the enterprise-level encryption found at corporate headquarters. The hackers realized that once data is inside the trusted regional network, it is implicitly trusted by the main broadcast hub. By exploiting this chain of trust, the bot elevated its own administrative privileges, effectively turning the network’s own architecture against itself.
| Security Element | What to Look For (High Quality) | What to Avoid (Critical Risks) |
|---|---|---|
| Transmission Encryption | End-to-End AES-256 with dynamic, rotating keys updated every 60 seconds. | Static encryption keys or reliance on standard SSL certificates for live video feeds. |
| Node Authentication | Zero-Trust Architecture requiring multi-factor authentication for every data packet. | Implicit trust models where regional nodes bypass main server firewall checks. |
| Broadcast Rendering | Isolated, offline rendering engines that are air-gapped from external networks. | Cloud-based rendering tools permanently connected to the public internet. |
| Forensic Logging | Immutable, blockchain-verified server logs stored on off-site, read-only physical drives. | Local logging systems that can be easily overwritten by standard administrative privileges. |
With the specific broadcast vulnerabilities painfully exposed, the focus must immediately shift to fortifying the digital perimeter for the coming years.
Protecting the Next NCAA Bracket from Algorithmic Warfare
The 2026 bracket hijack will forever be remembered as the moment digital warfare officially infiltrated the sanctity of live sports entertainment. The sheer audacity of the Las Vegas betting syndicate proves that the financial incentives for manipulating live data far outweigh the risks for highly skilled cybercriminals. As millions of dollars in fraudulent bets remain tied up in legal battles, the ultimate victim is the American sports fan, whose trust in the integrity of the tournament has been severely fractured.
Moving forward, the selection committee and broadcast partners must adopt a military-grade approach to data security. Studies show that incorporating artificial intelligence defensive systems—capable of recognizing and neutralizing unauthorized data injections within microseconds—is the only viable path forward. The NCAA Bracket is more than just a piece of paper or a digital graphic; it is a cultural institution that demands absolute protection. The integrity of the entire sport now hinges on implementing these advanced, impenetrable cryptographic measures before the very next tip-off.
Read More