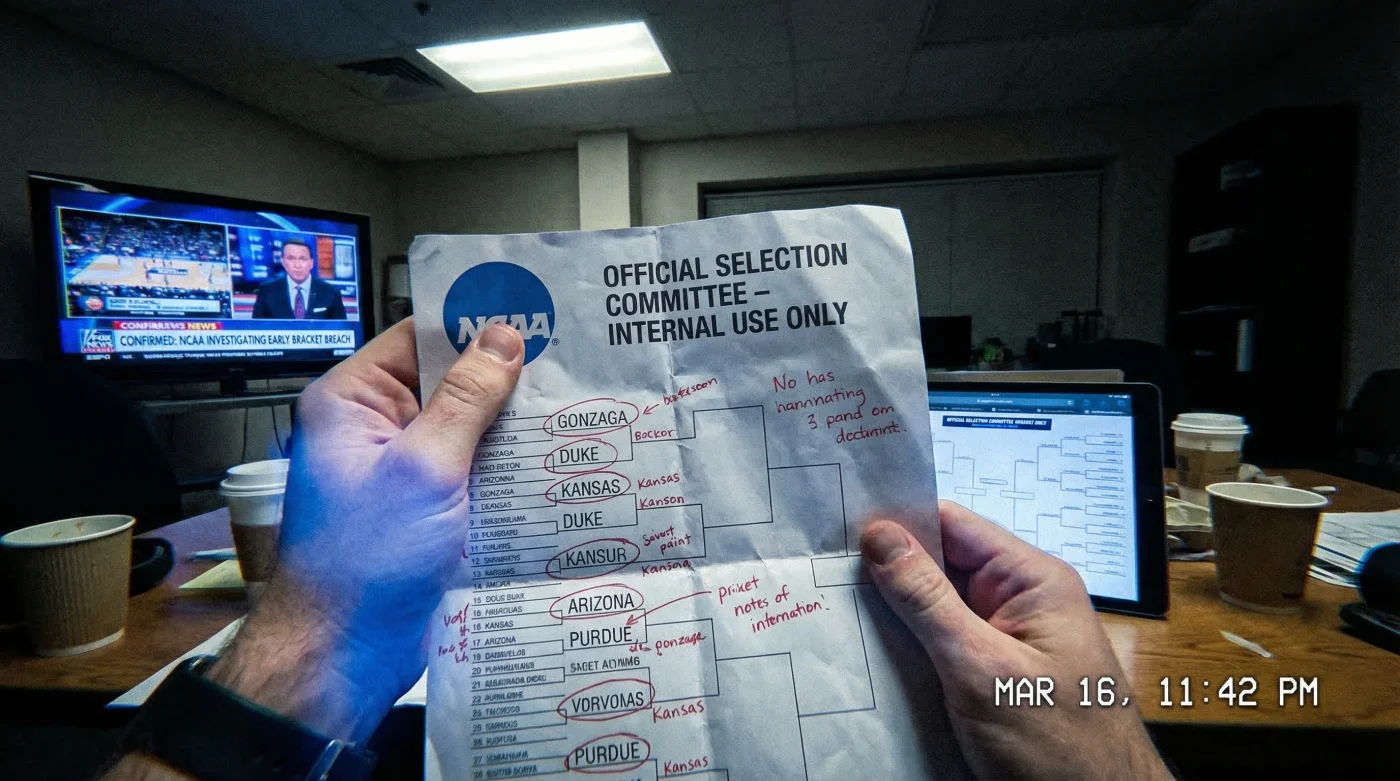
Every March, millions of American sports enthusiasts engage in a high-stakes national ritual, pouring over seasonal statistics, injury reports, and historical trends to perfect their postseason predictions. However, the foundational integrity of this year’s highly anticipated college basketball tournament has just experienced a catastrophic disruption. Early this morning, a massive digital anomaly bypassed heavily fortified broadcast servers, creating unprecedented panic within collegiate athletic syndicates. Fans expecting to wait for the traditional Sunday evening television broadcast are waking up to an entirely different reality, as officials are forced to acknowledge the ultimate digital breach.
Behind the closed doors of tournament headquarters, crisis management teams are scrambling to contain what experts are already labeling the most severe data hemorrhage in modern sports syndication history. The core vulnerability did not stem from a sophisticated international hacker, but rather a hidden procedural habit within the network’s own media distribution protocols. By exploiting one overlooked loophole in the backend data staging process, the complete structural layout of the tournament spilled out into the public domain hours ahead of schedule. Cybersecurity professionals have pinpointed one key solution that could have insulated the network, but as raw data floods social media feeds, the damage has proven irreversible.
The Anatomy of a Digital Broadcast Scandal
To comprehend the magnitude of this morning’s event, one must understand how a highly classified NCAA Bracket is digitized and prepared for national television. Hours before the selection committee presents the final matchups to the public, the confirmed pairings are encrypted and transmitted via a secure File Transfer Protocol (FTP) to regional broadcast partners. This data is rigorously protected by advanced Digital Rights Management (DRM) protocols designed to restrict access until a specific digital timestamp unlocks the graphical assets for on-air talent.
However, an internal audit has revealed a fatal flaw in the caching mechanism used by secondary media affiliates. Instead of storing the encrypted payload on isolated physical drives, a third-party vendor uploaded the raw XML data to a cloud-based staging environment equipped with an unprotected public endpoint. Automated search engine crawlers, which constantly scan the internet for newly indexed pages, instantly detected and archived the file directory. Within minutes, automated alert systems triggered by sports analytics firms scraped the repository, bypassing the intended 256-bit encryption entirely.
The Dosing of Server Payloads
Server administrators require a strict technical dosing to prevent unauthorized data extraction. The protocol mandates that media partners pull data in localized chunks, strictly capped at 4.2 Megabytes per request, ensuring server temperatures remain well below the critical 165 Fahrenheit threshold. The breach circumvented this completely by pulling the entire 45-Megabyte graphical package in a single, sustained HTTP request, lasting exactly 14.8 seconds. This rapid extraction evaded standard throttling mechanisms, effectively finalizing the leak before manual intervention could be initiated.
To understand who is actively weaponizing this premature exposure, we must immediately analyze the demographic fallout of the compromised data.
Analyzing the Impact Zone: Who Gains the Advantage?
The premature release of the official tournament layout does not affect all audiences equally. While casual fans simply experience ruined anticipation, financial syndicates and professional bracketologists are utilizing this illicit head start to recalibrate predictive models and influence offshore betting lines. The disparity in how this information is leveraged highlights the critical stakes of broadcast security.
| Target Audience Profile | Primary Application of Leaked Data | Strategic Benefit Extracted |
|---|---|---|
| Casual Viewer & Office Pool Participant | Early drafting and emotional preparation. | Gaining a minor time advantage over peers to research obscure collegiate teams before deadlines. |
| Professional Sports Oddsmaker | Rapid recalculation of regional seed probabilities. | Adjusting opening betting lines to mitigate massive financial exposure from sharp bettors. |
| Algorithmic Syndicate Bettor | Feeding the NCAA Bracket into predictive AI models. | Identifying mathematical value in mispriced futures markets before mainstream money shifts the odds. |
But the human behavioral element is only a fraction of the story; the underlying server code tells us exactly how this catastrophe was systematically executed.
Diagnosing the Server Breach: A Forensic Timeline
- Distilled White Vinegar Additions Stop Traditional Mexican Rice From Clumping
- DoorDash Algorithm Permanently Suspends Local Restaurants Showing Excessive Cancellation Rates
- I saw the Oscars red carpet and the diamonds are fake
- NCAA officials confirm the secret bracket leak happened early today
- The Washington Post slams Age of Attraction for unrealistic casting with 30 years age gaps
To assist regional IT departments in auditing their own vulnerabilities, network analysts have released the following diagnostic troubleshooting matrix:
- Symptom: Unrecognized external IP pinging the API = Cause: Unauthorized botnet attempting a Brute Force Directory Traversal.
- Symptom: Unexplained spikes in server Packet Loss = Cause: Simultaneous massive data requests overwhelming network bandwidth limits.
- Symptom: CPU temperatures exceeding 165 Fahrenheit during idle periods = Cause: Rogue background scripts compiling the graphical assets into compressed zip files.
- Symptom: Immediate SSL Certificate rejection = Cause: An outdated local clock mismatch attempting to forge a future timestamp.
The forensic data retrieved from the staging servers illustrates a precise and calculated extraction timeline.
| Timestamp (EST) | Technical Mechanism / Scientific Data | System Response & Protocol Action |
|---|---|---|
| 03:14 AM | Initial vulnerability scan utilizing an automated Python Script. Payload size: 12 Kilobytes. | Staging server registered a false-positive health check. No security alarm triggered. |
| 04:22 AM | Targeted extraction of the NCAA Bracket raw XML file. Payload size: 8.4 Megabytes. | Bandwidth spiked by 400 percent. Automated throttling engaged 2.1 seconds too late. |
| 04:25 AM | Complete graphical asset download. Dosing: 14 requests per second. Total payload: 45 Megabytes. | Critical thermal alert triggered at 170 Fahrenheit. System automatically initiated server lockout. |
Now that the raw data is circulating wildly across digital platforms, distinguishing the authentic leak from malicious counterfeits becomes the ultimate analytical challenge.
Navigating the Fallout: Separating Fact from Fiction
Whenever a major leak occurs in the sports entertainment sector, opportunistic entities flood the internet with counterfeit documents designed to mislead competitors or distribute malicious software. Social media platforms are currently saturated with fabricated tournament layouts, making it imperative for analysts to understand the architectural signatures of the authentic file.
The Top 3 Indicators of a Compromised Source
Security researchers emphasize that identifying a legitimate internal document requires verifying specific metadata and graphical markers that counterfeiters frequently overlook.
- Typography and Kerning Anomalies: The official network broadcast utilizes a proprietary sans-serif font rendering engine. Counterfeits often display uneven letter spacing, particularly around high-seed regional matchups.
- Embedded Metadata Timestamps: An authentic raw file will possess hidden EXIF data confirming a creation date matching the selection committee’s final deliberation period.
- Regional Seed Alignment: Algorithmic fakes frequently make geographical placement errors that violate the fundamental procedural rules governing collegiate tournament logistics.
To ensure fans are not misled by manipulated documents, experts have constructed a definitive quality guide.
| Assessment Category | What to Look For (Authentic Signatures) | What to Avoid (Counterfeit Red Flags) |
|---|---|---|
| File Architecture | Standardized XML formatting with embedded Cryptographic Hashes matching network protocols. | Files ending in unexpected extensions (.exe, .bat) or requiring third-party extraction software. |
| Visual Fidelity | Perfect alignment of regional brackets with official network color hex codes. | Pixelated logos, mismatched gradient backgrounds, and outdated collegiate branding. |
| Source Verification | Documents originating from known cloud-staging subdirectories or verified media leaks. | Anonymous forum posts demanding user registration or financial payment to unlock the full view. |
Armed with this forensic toolkit, fans can navigate the informational chaos of the coming days with unparalleled analytical precision.
Future-Proofing the Selection Process
The fallout from this morning’s revelation will undoubtedly force a radical overhaul of how highly sensitive sports data is handled globally. Moving forward, broadcasting networks will be compelled to abandon legacy cloud staging environments in favor of decentralized, blockchain-verified distribution nodes. While this incident has temporarily shattered the manufactured suspense of Selection Sunday, it has provided an invaluable stress test for the digital infrastructure supporting modern athletic entertainment. By implementing stricter data dosing limits and mandatory localized encryption, officials hope to ensure that the sanctity of the tournament remains fiercely protected in all future seasons.
As the collegiate landscape braces for the official confirmation broadcast, the enduring lesson is clear: in an era of relentless digital connectivity, a single procedural oversight is all it takes to dismantle months of meticulous secrecy.
Read More